If You Virtualize Applications and Windows Desktops with VMware, You’ll Love How Easy it is to Configure, Deploy, Manage and Secure Policies and Settings with PolicyPak
Virtualize Windows desktops and their respective apps, and then lock them down with the power of PolicyPak. Simplify, fix, and control issues around UAC prompts, Windows 10 & 11 File Associations, the Start Screen & Taskbar, enterprise applications, internet browsers, and more!
Manage and Secure VMware Workstation Virtual Desktops
PolicyPak enforces and locks down the optimum settings that your organization requires. PolicyPak also sets and applies the settings that your users expect, so they get the same experience as if they were at a local machine. With PolicyPak, rest assured that your VMware Workstation configuration settings will stay consistently enforced.
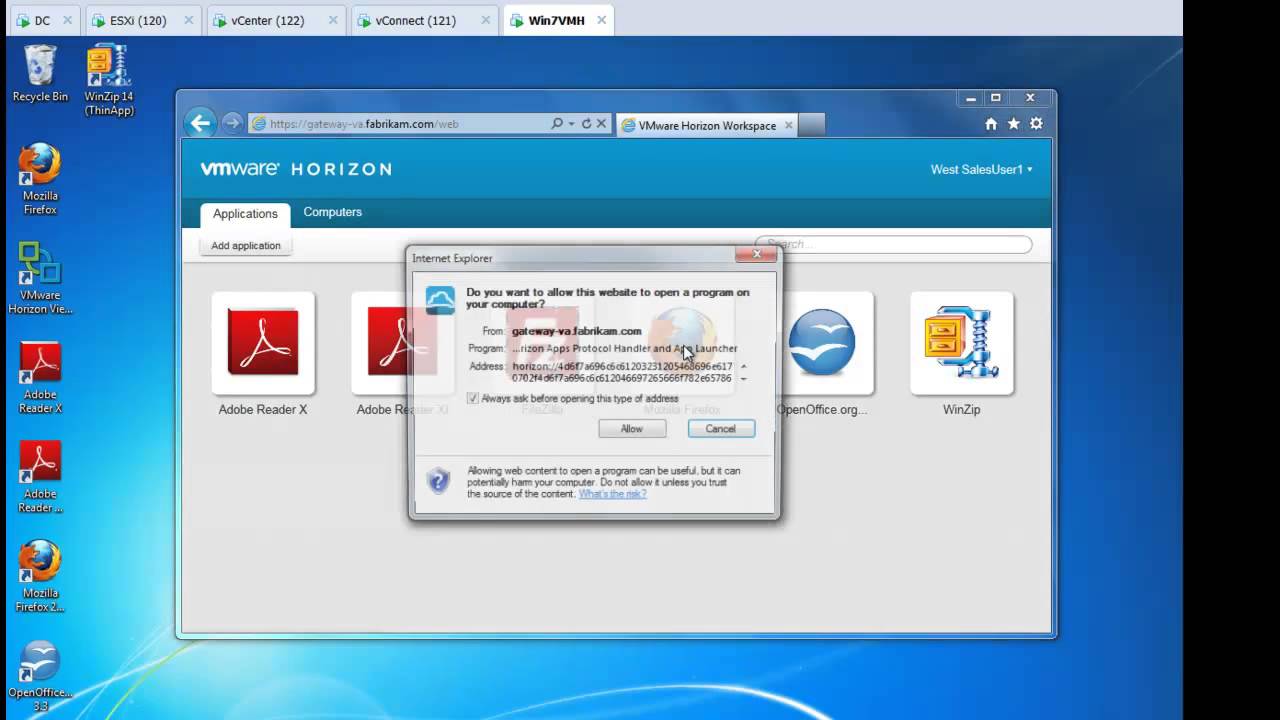
Manage and Secure VMware Horizon Virtual Apps
VDI is awesome… until you’re trying to really manage all your applications, browsers and Java or Windows 10 & 11 & 11 settings like Start Screen, Taskbar and File Associations. When you add PolicyPak you’re making VMware Horizon instantly more powerful.
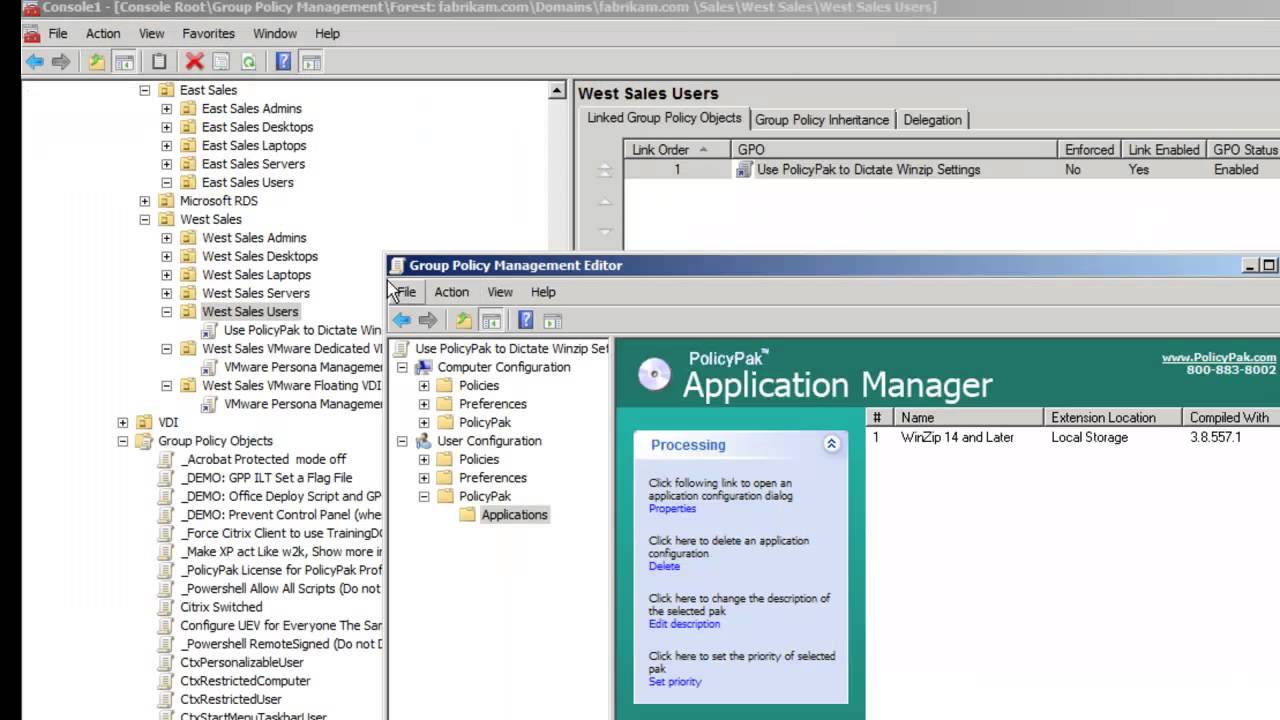
Manage Application Settings
With VMware Horizon, users get the apps they need, but you’ve got zero control over settings and configurations. With PolicyPak, you have full control over application settings, ensuring that apps are locked down and managed per your security and compliance requirements.
Manage ThinApp Application Settings
After deploying ThinApp applications and making them available for usage, you have no easy way to manage and lockdown settings and policies. PolicyPak simplifies ThinApp application management and security by ensuring their configurations are consistently enforced and automatically remediated.