Jeremy Moskowitz founded PolicyPak Software after working with hundreds of customers with the same problem they couldn’t manage their applications, browsers and operating systems using the technology they already utilized.

Prevent Sodinokibi Ransomware from Infecting Your Enterprise
Preventing Sodinokibi Ransomware and similar strains require a combination of software and knowhow. In this blog, we’ll review both, so you can confidently build out your cybersecurity program.
Cost of Ransomware
The cost of Ransomware is rising astronomically. According to an article published by Bankinfosecurity.com, the average ransomware payment increased to $36,292 in Q2 of 2019 from $12,762 in Q1 of 2019. That’s a spike of 184 percent! The average downtime also increased from 7.3 days to 9.6. The trends are heading in a negative upward spiral.

So why the dramatic increase?
What is Sodinokibi Ransomware?
The culprit is a new strain of Ransomware called Sodinokibi, also referred to as Sodin and Revil. As far as malware, Sodinokibi is an infant as it is barely three months old at the time of this writing. Despite it being the new kid on the block, Sodinokibi is wreaking havoc across the country, primarily on government institutions.

Where did Sodinokibi Originate?
Security experts believe that Sodinokibi is the apparent heir to a strain known as GrandCrab. The security community believes GrandCrab is responsible for 40 percent of all ransomware infections globally. It has taken in around $2 billion in ransom. Then earlier this year, the creators of GrandCrab announced the malware’s retirement.

Said the site’s administrator:
“We are getting a well-deserved retirement,” the GrandCrab administrator(s) wrote in their farewell message on May 31. “We are living proof that you can do evil and get off scot-free.”
Sodinokibi, the Heir Apparent to GrandCrab
While many heaved a sigh of relief, any sense of reprieve appears to have been short-lived, as it appears that the same developers of GrandCrab are behind Sodinokibi. Like GrandCrab, the Sodinokibi gets distributed via Ransomware-as-a-Service (RaaS). Meaning, the developers can now make the malware available to affiliates to use in their attacks. In exchange, the developers retain 40 percent of all initial ransom payments. Once an affiliate garners three payments, their cut rises to 70 percent.
In the same way that subsequent software releases continue to get better, Sodinokibi is more developed than its predecessor is. It is highly evasive and can take measures on its own to prevent its detection by antivirus and other layered security measures. The primary delivery mechanism for Sodinokibi uses targeted phishing attacks. One example is a spam campaign that pretends to come from Booking.com. The emails carry an attached document that, when clicked, opens an executable code loader. While it elusively infiltrates your network, it prominently announces its presence by modifying the desktops of the infected network and alerts users that their files are encrypted.
Sodinokibi Victims
It is hard to believe that a single mouse click can be worth $500,000, but in this case, it’s true. Sodinokibi first began appearing in late April 2019, and a month later appeared in two separate attacks on Florida towns. The City of Riviera Beach, Florida, agreed to pay $600,000 for the decryption key to unlock their files. Weeks later, the city of Lake City, Florida, relented to a $450,000 ransom payment as well. Each of these cities faced service disruption after being infected. Some of these services included email, phones, police records, the public works department, the library, 911 emergency, and general offices. Because these towns do not have the personnel or knowledge base to remediate these attacks, paying the ransom seemed to be the best bet.

It isn’t just the Sunshine State that experienced the fury of Sodinokibi. After then making its way through Georgia, it hit the state of Texas in a big way. In a highly coordinated attack, hackers were able to bring down 22 separate municipalities, including the cities of Borger and Keene.
The perpetrators of the attack then asked for a collective $2.5 million to release everyone caught in the net. Fortunately, the infected Texas municipalities received state-issued resources from Texas A&M University and the Texas Military Department.
Stop Cryptocurrency-Mining Malware
Hackers have identified a number of ways to “mine” cryptocurrency, and one way is to use your business’s computers. There are a few ways to do this – through cryptomining malware and cryptojacking.
How to Prevent Sodinokibi Ransomware
Like most malware, Sodinokibi requires elevated privileges to install its payload. Unfortunately, organizations continue to allot local admin privileges to standard users, which makes it too easy for this menace.
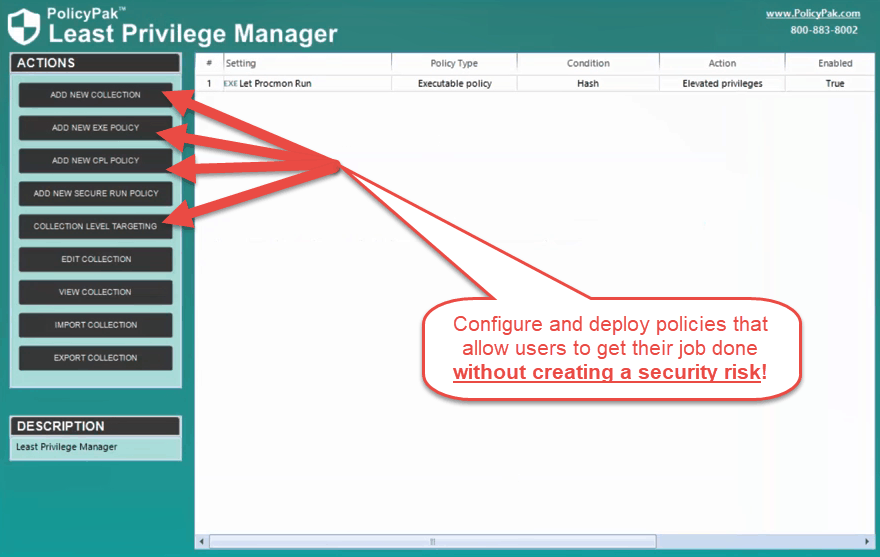
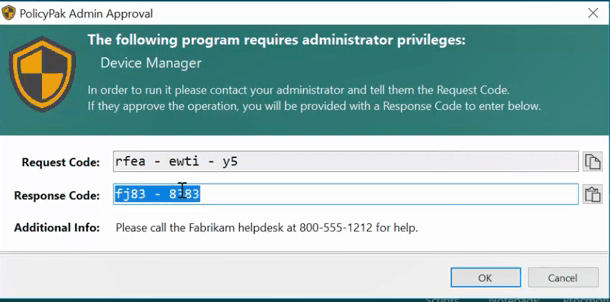
It does not have to be that way, however. With PolicyPak Least Privilege Manager, you can strip regular users of local admin rights, but give them limited admin privileges to do any designated tasks that may require elevated privileges. Use cases include installing an approved application, getting past a UAC prompt, or accessing individual control panel applets.
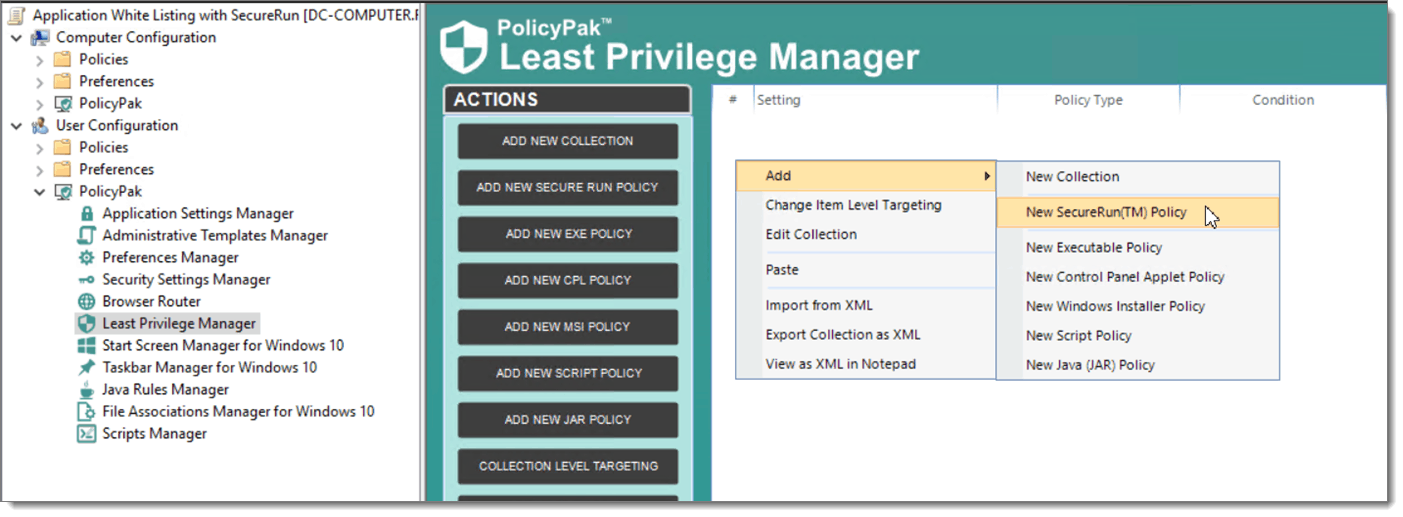
PolicyPak SecureRun™
It all starts with SecureRunTM, which is a part PolicyPak Least Privilege Manager. The premise behind SecureRun™ is simple: if an application isn’t installed properly by an administrator or someone on the SecureRun™ Member list, it cannot run. Whether it is a bank trojan, a ransomware strain, a video game, or an unlicensed or unapproved software application, if it was installed or attempted to run by a standard user, not on the SecureRun™ member list, it is blocked.
Using SecureRun™
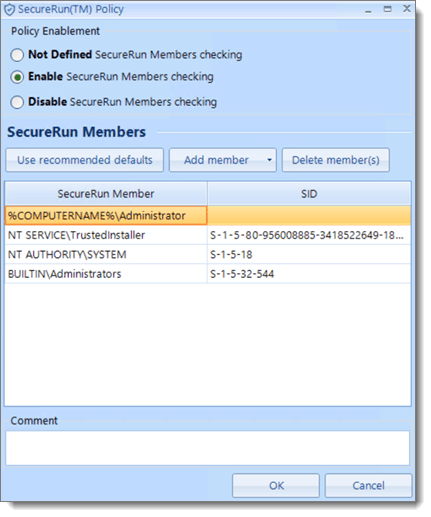
An example of the SecureRun™ member list is shown below.
Below is the default SecureRun membership list. You can add or delete members according to your individual security needs. Typically, the PolicyPak SecureRun defaults are enough for most organizations.
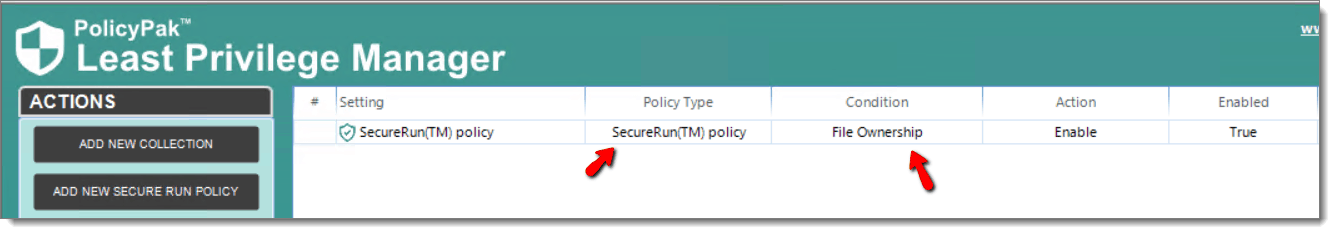
And so, a SecureRun policy is then created using the file ownership condition.
With Admin rights banished and SecureRunTM in place, you use PolicyPak Least Privilege Manager to create policy rules so that users can perform selected privileged tasks. Often this means installing applications, so let’s use this as an example. Start by creating a policy for your users that includes a rule or rule set to accommodate designated applications. Since PolicyPak integrates with Group Policy Editor, administrators are already familiar with the technology and can complete the task quickly.
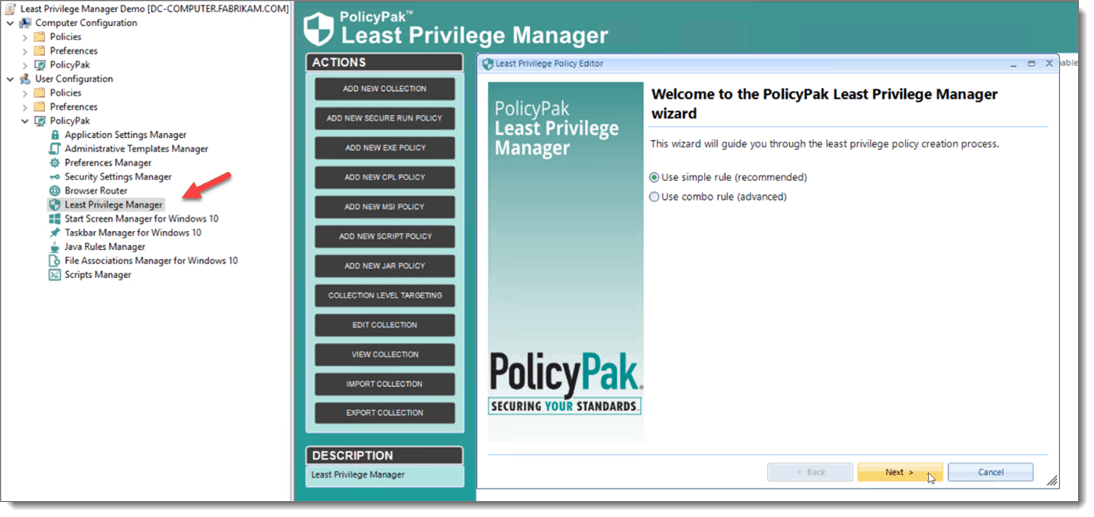
The rules coincide with one or more criteria, based on the designated EXE or MSI install file. Criteria can include the name or location (called the Path), the fingerprint of the file (called the Hash), which company digitally signed the file (called the Signature), or specific characteristics of a file like Version and inner name (called File Info). Once you deploy your policy, any application matching the described criteria can get installed by standard users in a usual fashion. An example of the criteria selection process is shown below.

You see a video demonstration of how to let standard users install MSI applications when needed, click here.
Maybe you need to give standard users access to individual Control Panel applets. Again, create a Control Panel Applet policy using PolicyPak Least Privilege Manager. Then choose the applet that you want to run with elevated privileges. The result is that standard users gain uninhibited access to any Control Panel applet you choose.

Believe it or not, we’ve only scratched the surface potential of PolicyPak Least Privilege Manager. A couple of other capabilities worth noting include:
- Overcome Network Card, Printer, and Add/Remove Programs UAC prompts (Click here to see a video demonstration of this capability)
- Block or allow Windows Universal applications (Click here to see a video demonstration of this capability)
- Block “Living off the land” attacks with PowerShell (Click here to see a video demonstration of this capability.)
Final Thoughts
While we may have only scratched the surface concerning the many solutions contained within our PolicyPak suite of solutions, the goal is to prevent Sodinokibi from infecting any of the surfaces within your enterprise. The goal is easily attainable with PolicyPak and doesn’t require the burdensome task of updating application whitelists, blacklists or perpetually downloading new signatures.