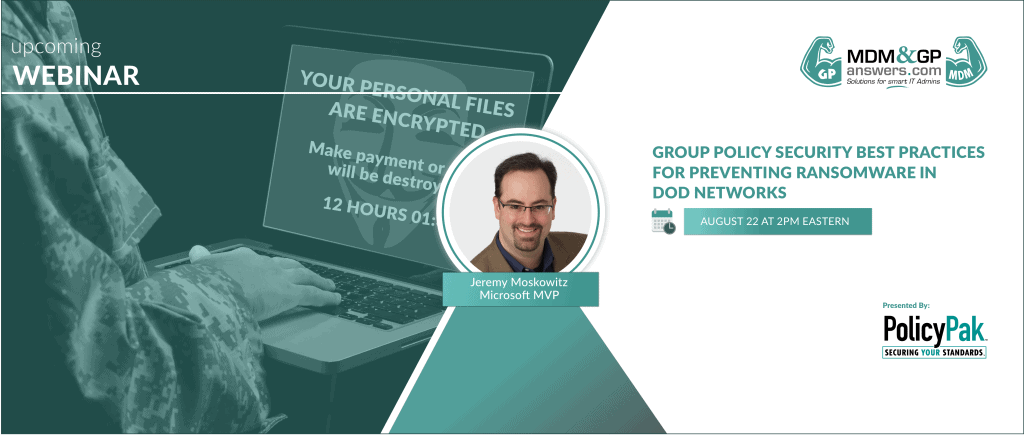
Group Policy Security Best Practices for Preventing Ransomware in DOD Networks
The Department of Defense provides the military forces needed to deter war and ensure our nation’s security. However, today’s domestic and foreign cyber terrorists jeopardize American defense systems using ransomware and other malicious malware.
According to the Department of Homeland Security, more than 4,000 ransomware attacks have occurred daily since January 1, 2016. Moreover, the Department of Homeland Security states that “Prevention is the most effective defense against ransomware and it is critical to take precautions for protection.” In accordance with the department’s Ransomware Executive One-Pager and Technical Document, preventative measures include the following:
- “Manage the use of privileged accounts based on the principle of least privilege: no users should be assigned administrative access unless absolutely needed; and those with a need for administrator accounts should only use them when necessary.”
- “Implement Software Restriction Policies (SRP) or other controls to prevent programs from executing from common ransomware locations, such as temporary folders supporting popular Internet browsers or compression/decompression programs, including the AppData/LocalAppData folder.”
AUGUST 22, 2019 AT 2PM EASTERN
Join Jeremy Moskowitz, 15-Time Microsoft MVP awardee for Endpoint Management and Enterprise Mobility, for a free 60-minute webinar on Group Policy Security best practices for preventing ransomware. During this webinar, you’ll receive 100% free group policy security tips taken directly from Jeremy’s award-winningGroup Policy training program. Plus, you’ll learn how Group Policy Administrators around the country use PolicyPak to protect their Windows networks from ransomware attacks.
Group Policy Security Best Practices for Preventing Ransomware in DoD Government Networks covers the following topics:
- Delegating Permissions over Group Policy usage
- Default GPOs and Fine-Grained Password Policy
- AppLocker, DeviceGuard & PolicyPak Least Privilege Manager
- LAPS: Local Admin Password Solution
- Application and Browser Security using PolicyPak
ABOUT THE SPEAKER
Jeremy Moskowitz is a 15-time Microsoft MVP awardee for endpoint management and enterprise mobility using Group Policy and Modern Device Management. Jeremy’s published works include Group Policy: Fundamentals, Security and the Managed Desktop (Copyright © 2015 by John Wiley & Sons., Indianapolis, Indiana) and MDM: Fundamentals, Security and Modern Desktop (Copyright © 2019 by John Wiley & Sons., Indianapolis, Indiana). Jeremy Moskowitz is the CEO and head instructor for MDMandGPanswers.com, which has enrolled over 16,000 students and is the founder of PolicyPak Software, which manages and protects nearly 2 Million endpoints worldwide.

