Jeremy Moskowitz founded PolicyPak Software after working with hundreds of customers with the same problem they couldn’t manage their applications, browsers and operating systems using the technology they already utilized.

Top 6 Windows Security Settings To Configure Right Now
Do You Have These 6 Windows Security Settings Set Up?
Windows security settings can help secure domain controllers, servers, clients, and other resources in your organization. Without Windows security settings, you would be unable to authenticate users, limit access to resources, manage group membership, or audit changelogs. Microsoft designed Windows security settings to combat the dynamic nature of cybersecurity. It is the Windows-as-a-service architecture that provides Microsoft the ability to perpetually innovate security technologies to ensure that Windows 10 remains their most secure operating system to date. Below are some of the top Windows security settings that are designed to keep you safe.
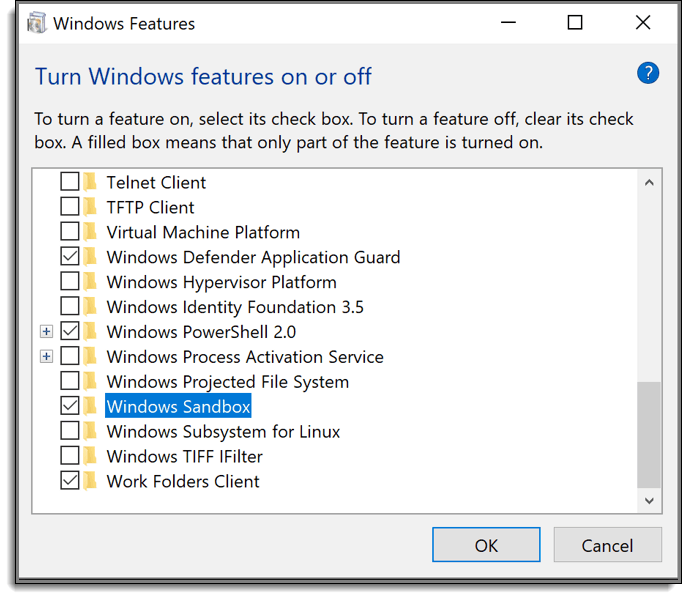
Windows Security Setting #1: Windows Sandbox
Sandboxing is a security tool found in many Next-Generation Firewalls (NGFW) and cloud-based email security solutions. A security sandbox is a safe, isolated area where you can open suspicious files and URLs. Should the suspicious culprit contain malicious code, the malware is allowed to do its thing in a quarantined environment. Microsoft just released Windows Sandbox for Windows 10 in the Windows 10 1903 release. The new security tool provides an isolated virtual environment where you can run executables or untrusted software without affecting the host PC. No matter what nasty malicious code may be embedded, everything stays in the sandbox. You must enable Windows Sandbox in Windows Features, and your computer must support virtualization, or the option appears grayed out. With Windows Sandbox, you don’t have to fret over the fear of running a downloaded app or executable file.
Windows Security Setting #2: Windows Updates
New security features such as Windows Sandbox wouldn’t be possible without the Windows 10 update feature. While it is not a dedicated security tool, it’s one of the most important security features of the operating system, allowing your devices to get the latest fixes and security improvements. With the new 1903 release, Microsoft announced the use of AI to improve the update process. You can delay updates in an enterprise environment by either scheduling them or pausing them temporarily. For even greater control, updates can be managed in enterprise environments using Windows Updates for Business, which utilizes the assignment of servicing rings to different types of users. Keeping your machines updated is a top security priority today. The only downside to using Windows updates is the raw number of GPOs that are required. Instead, however, you can reduce those GPOs and get the same experience with PolicyPak Admin Templates Manager.
Windows Security Setting #3: Windows Security
Formerly known as Windows Defender Security Center, Windows Security is the primary hub that hosts many of the key security tools san settings for protections areas such as antivirus, local firewall, and app and browser control. Windows Security works continuously to protect Windows 10 devices from malware, viruses, and cyber-attacks. Real-time protection updates are also downloaded automatically to combat the latest threats. Should you choose to install a third-party antivirus or firewall solution, the center automatically becomes the secondary line of defense. You can see the complete list of Windows Security protection areas below.

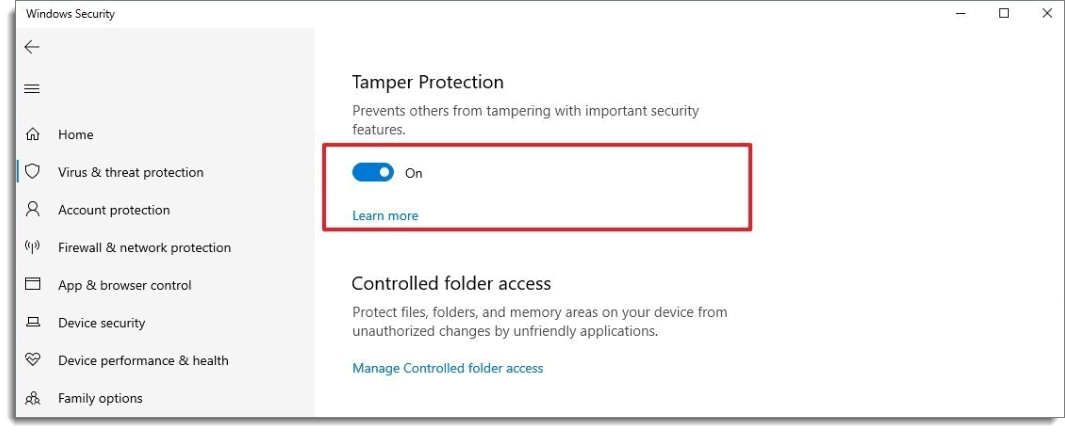
Windows Security Setting #4: Tamper Protection
Another new security feature introduced in the Windows 10 1903 release is Tamper Protection. Tamper Protection is turned off by default so it must be enabled first to take advantage of it. Tamper Protection prevents malicious apps from changing critical Windows Defender Antivirus settings. This feature is important because advanced malware is now integrated with built-in intelligence that can seek out and modify antivirus software settings. Keep in mind that Tamper Protection only secures the Windows Security app, so it doesn’t apply to third-party antivirus programs.
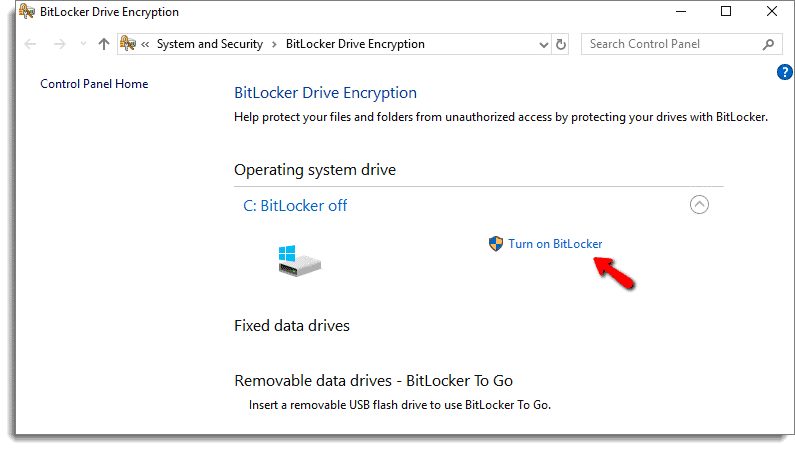
Windows Security Setting #4: BitLocker
Several years ago, a large organization was forced to pay out a significant settlement concerning a class-action lawsuit concerning the personal data that was obtained from a stolen laptop computer. Even to this day, organizations remain susceptible to data compromise because of lost or stolen laptops. To help thwart this, Microsoft first introduced BitLocker in some editions of Windows 7. Today it is offered in all Windows 10 editions other than Home. BitLocker encrypts your entire drive, and the process is pretty much invisible as you are unable to discern any difference once you enable it. Any mobile Windows 10 computer that hosts sensitive data should be protected by BitLocker, which you can manage through either Group Policy or Intune.
Windows Security Setting #5: Privacy Settings
By default, the big tech firms want everyone to share everything. Fortunately, Microsoft gives you the ability to decide what you are willing to share on your Windows 10 device. Some of the more important settings include the following:
- Enable/disable advertising and location tracking
- Restrict access to the camera and microphone (screenshot below)
- Manage which apps have access to your contacts, email, and calendar
- Restrict access to your account information on your device
Get More Windows Security Settings with PolicyPak
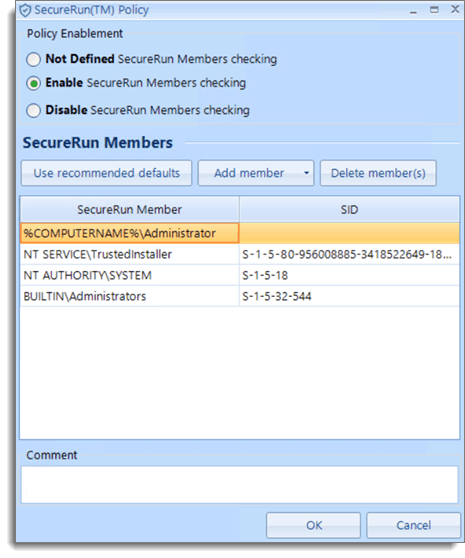
Considering the plethora of cyberattacks today and the continual release of new threats, you can’t be too secure. While Windows 10 provides some excellent security offerings, there are still gaps. For instance, antivirus solutions provide little protection against zero-day malware attacks. That’s why many companies are considering application whitelisting solutions as a way to ensure that everything but approved “good activity” is blocked. The problem, however, is that traditional whitelisting solutions require constant updating to the approved application list. Then there’s the ordeal of managing multiple lists for different types of users and computers. Wouldn’t it be great if there were a “one-click” solution?
Well, there is. PolicyPak SecureRun offers an entirely new approach. It’s a part of PolicyPak Least Privilege Manager, and it works on a ridiculously simple premise that if an application wasn’t installed properly by an administrator or someone on the approved SecureRun Member list, it wouldn’t run at all. Are you ready for the one-click? Well, like most of the PolicyPak suite of components, it all starts with the creation of a policy using Group Policy Editor.

Moreover, if the default member list works for you, everything is done.
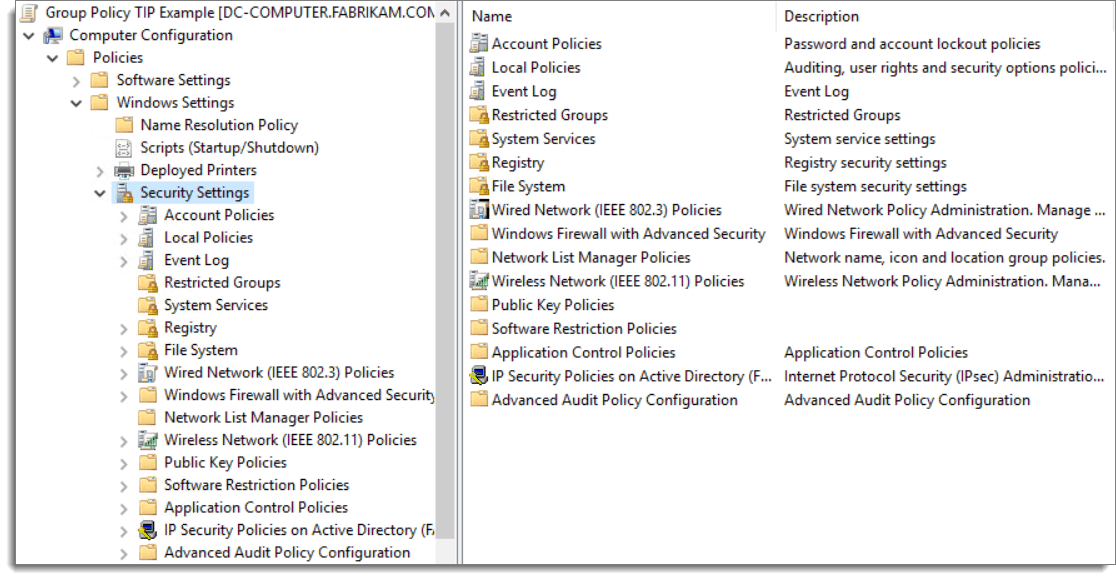
Let’s cover one more PolicyPak Security solution option. As any Group Policy administrator knows, there are lots of useful Security Settings available under the Windows Settings group of policies as is shown in the screenshot below.
The problem is that group policy security settings can only deploy to objects within a domain. What about computers that aren’t domain-joined? It means that you can’t enforce the vital policies concerning password settings, account lockout policies, or user rights assignments. Fortunately, there is a way to centrally manage these types of settings for any Windows computer on your network, on-prem, off-prem, domain-joined or not.
PolicyPak Security Settings Manager gives you the ability to deploy most of the security settings found in Group Policy and deploy them through MDM, SCCM, or PolicyPak Cloud Edition. Again, the process is easy. Start by configuring your desired security setting policies and then export them using the PolicyPak Security Settings Manager as is shown below.
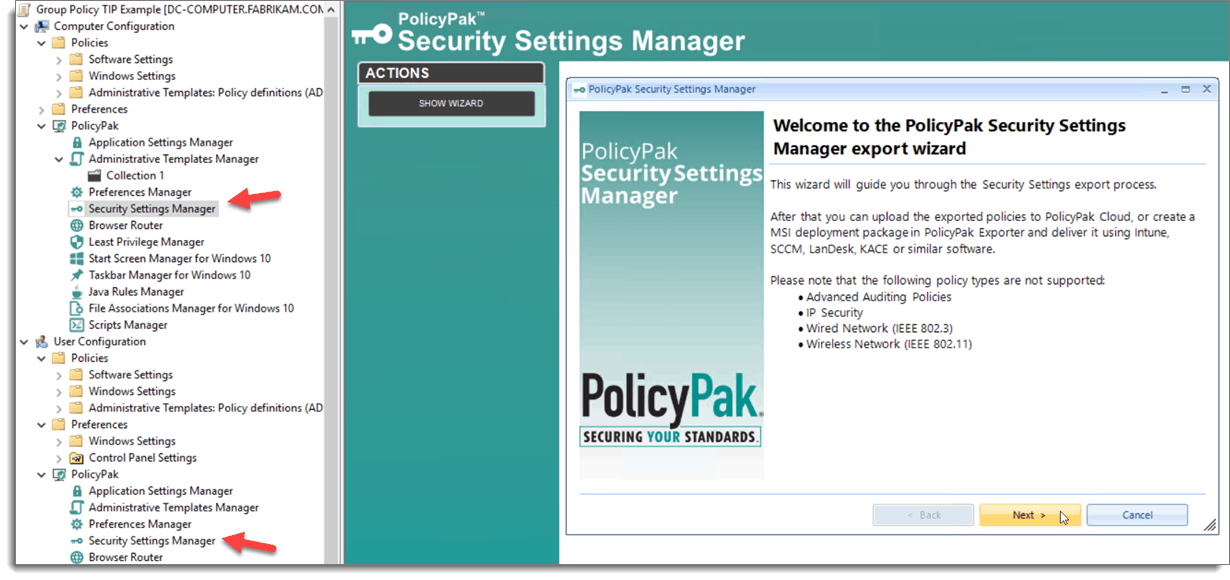
This process exports your settings into an MSI file that you can then deploy using your preferred systems management solution. With PolicyPak, robust security isn’t just limited to domain-joined machines.
By pairing the existing security settings of Windows 10 with the super security admin powers of PolicyPak, you and your management team can rest a lot easier knowing that your systems are indeed locked down. Cybersecurity may be a moving target, but the culmination of Windows 10 and PolicyPak can ensure you always hit the bull’s eye when it comes to protecting your devices.


